Intelice Solutions: Blog
Trick or Treat: How Hackers Use Social Engineering to Gain Access
Social engineering attacks are some of the most effective tricks used by cybercriminals. By manipulating human emotions like trust, urgency, or fear, hackers deceive individuals into giving up confidential information or access to secure systems. From phishing emails to impersonating…
Read MoreMaximize Your IT Budget: Start Planning Now
As we move deeper into 2024, now is the ideal time to review and optimize your IT budget. A well-planned budget not only ensures your IT infrastructure operates smoothly but also positions your business to adapt to emerging technologies and…
Read MoreLocal IT Support in Washington
Intelice Solutions specializes in providing customized IT solutions to address various industries within the Washington metropolitan area. The legal industry necessitates robust data security and unwavering adherence to confidentiality standards. Our services include secure electronic health record systems and robust…
Read MoreStrengthening Your IT Infrastructure for Year-End Demands
As we approach the final quarter of the year, businesses across all industries often face a surge in activity. Whether it’s closing deals, processing data, or ramping up production, the demands on your IT infrastructure can escalate quickly. Ensuring that…
Read MoreIT Support Company in Washington: Nation’s Capital Tech Partner
Intelice Solutions is a leading IT support company in Washington. As the nation’s capital presents a dynamic and complex technological environment, our solutions are meticulously tailored to address the unique IT challenges faced by businesses within the city. Our comprehensive…
Read MorePreparing for a Cyber-Safe School Year: Essential IT and Cybersecurity Tips for Students and Parents
As the new school year approaches, students and parents are gearing up for a fresh start. Technology plays a crucial role in education, making it imperative to prioritize IT and cybersecurity. Ensuring that devices and online activities are secure can…
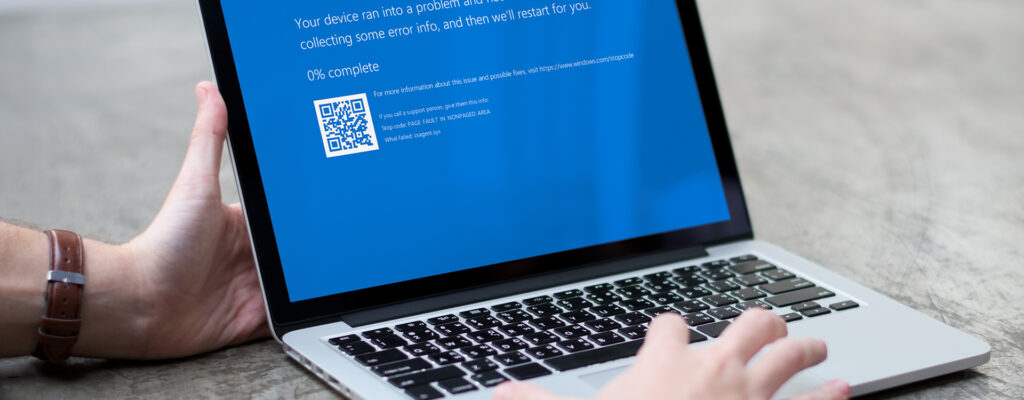
Read MoreLessons to Learn from the CrowdStrike Outage
The recent CrowdStrike outage serves as a significant wake-up call for businesses relying on cybersecurity solutions. CrowdStrike’s temporary service disruption, as one of the leading providers of endpoint security, underscores the importance of preparedness and resilience in the face of…
Read MoreEmpowering SMBs with Tailored Business IT Services
As an IT services company, Intelice Solutions understands that small and medium-sized businesses (SMBs) in Washington rely on robust business IT services to maintain competitiveness. At Intelice Solutions, we specialize in managed IT services designed specifically for local enterprises. From…
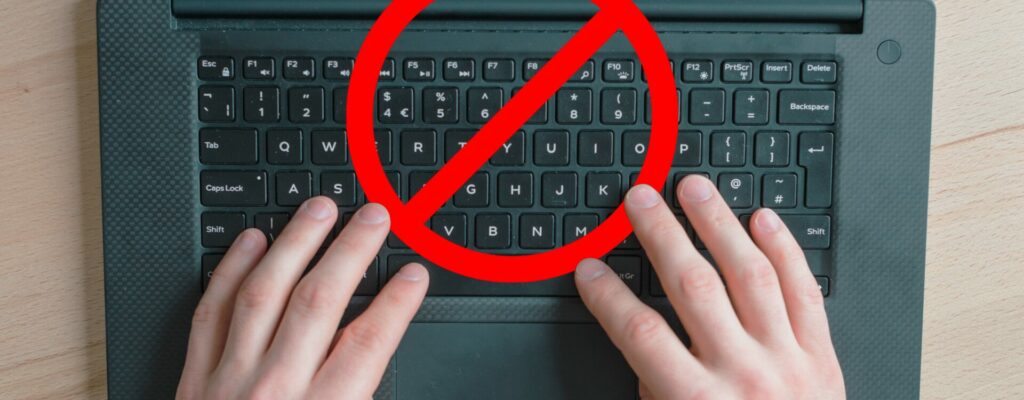
Read MoreMalware Alert: Beware of Copy-Paste Attacks!
A new warning for Google Chrome users has emerged, carrying a critical yet straightforward piece of advice: avoid copying and pasting unfamiliar text into your terminal or run dialog box. This advice comes from cybersecurity firm Proofpoint, which has identified…
Read MoreBoost Your Smartphone Security: Why the FBI Advises Regular Reboots Matter
Have you ever considered why your smartphone might benefit from a regular reboot? The Federal Bureau of Investigation (FBI) advises a simple yet effective practice: regularly rebooting your phone. This recommendation, backed by cybersecurity experts, plays a crucial role in…
Read MoreRecent Posts
How can we help?
Whether you need immediate help with an IT issue or want to discuss your long-term IT strategy, our team is here to help.
Call us at (301) 579-8066 or complete the form below and we'll help in any way we can.
"*" indicates required fields
Categories
- 2020's Rewrites
- Advanced Cybersecurity
- Blog
- Company News
- Compliance Articles
- COVID19
- Cybersecurity Alerts
- Cybersecurity Awareness Month – 2022
- Cybersecurity Insights
- Cybersecurity News
- Financial Management Systems
- Financial Management Systems
- Financial Management Systems ERP Solutions Articles
- General Business Insights
- Industry News
- Industry Reports
- Intelice Case Studies
- Intelice News & PR
- Intelice News & PR
- Intelice's Solution
- IT Services In Washington DC Metro
- Managed IT Services Articles
- Managed Security
- Meet The Team
- Microsoft 365
- Microsoft Business Central
- Microsoft Office
- Microsoft Teams
- Microsoft Tips & Tricks
- News
- Newsletter
- Optimize Blog
- Our Partners
- Tech Tips
- Technology Education & Information
- Testimonials
- Video Library
- Webinar Replay